A new and sophisticated hacker group, known as TeamPCP, is sowing chaos on the Internet with a persistent campaign spreading a novel, self-propagating backdoor, accompanied by a disturbing data wiper specifically targeted at Iranian machines. The visibility of this group first emerged in December, when security researchers at Flare observed the release of a worm designed to attack inadequately protected cloud platforms. The primary goal was to build a distributed proxy and scanning infrastructure, to then be used to compromise servers, exfiltrate data, distribute ransomware, conduct extortion activities, and even for cryptocurrency mining. TeamPCP stands out for its remarkable skill in large-scale automation and the integration of well-known attack techniques, demonstrating a capacity for constant evolution.
Relentless Campaign and Continuously Evolving Malware
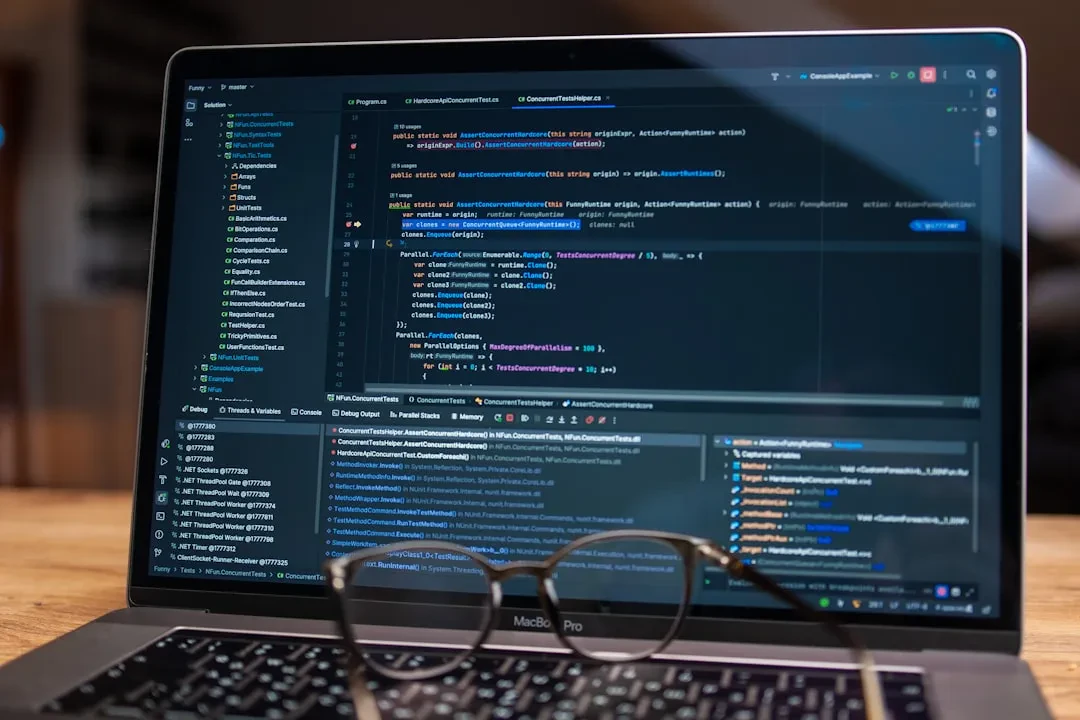
Recently, TeamPCP has intensified its offensive with an unrelenting campaign, employing continuously evolving malware to extend its control over an ever-increasing number of systems. Just last week, the group managed to compromise almost all versions of the widespread vulnerability scanner Trivy. This supply chain attack was made possible by obtaining privileged access to the GitHub account of Aqua Security, the company that created Trivy. Over the weekend, researchers reported the spread of a powerful malware by TeamPCP, equipped with worm capabilities, allowing it to automatically propagate to new machines without any user interaction. Once a machine is infected, the malware actively seeks npm repository access tokens, compromising publishable packages through the creation of a new version infused with malicious code. Aikido documented the targeting of 28 packages in less than 60 seconds. Initially, the attacker had to manually propagate the worm, but later versions eliminated this requirement, vastly expanding its reach.
An Innovative and Tamper-Proof Control Mechanism
The worm was controlled by an unusual mechanism, designed to be tamper-proof. It used a 'canister' based on the Internet Computer Protocol, a form of self-executing smart contract, designed to be impossible for third parties to take down or alter. This canister could point to constantly changing URLs for the servers hosting the malicious binaries, offering attackers a way to continuously update the command and control server addresses. Infected machines reported back to the canister every 50 minutes. Although the canister was subsequently deactivated, for a period it represented a significant threat. Like the previous TeamPCP malware, known as CanisterWorm, this one also attacks organizations' CI/CD pipelines, which are fundamental for rapid software development and release. Every developer or pipeline that installs this package and has an accessible npm token becomes an unwitting propagation vector, infecting their own packages and, consequently, downstream users.
The Unexpected Payload: The Kamikaze Data Wiper
As the weekend progressed, CanisterWorm was updated to include an additional payload—a data wiper that exclusively targets machines in Iran. Once machines are infected, the worm checks if the machine is in the Iranian time zone or configured for use in the country. In either case, the malware disables credential theft and activates a new wiper named Kamikaze by TeamPCP's developers. There are no indications yet that the worm has caused actual damage to Iranian machines, but the potential for large-scale impact is clear. Kamikaze's logic is simple and brutal: if the machine uses Kubernetes and is in Iran, it executes a command to delete all cluster nodes. If it uses Kubernetes but is not in Iran, it installs the CanisterWorm backdoor. If it does not use Kubernetes and is in Iran, it executes an `rm -rf / --no-preserve-root` command, which erases the entire system. In the absence of Kubernetes and outside of Iran, the malware simply does nothing. Targeting a country with which the United States is currently in conflict is a curious choice, given that TeamPCP's primary motivation has always been financial gain. Without a clear link to monetary profit, the wiper seems out of character for the group. There could be an ideological component, or a deliberate attempt to attract attention. By compromising security tools and open-source projects, TeamPCP is sending a clear and deliberate signal.
The Ongoing Vulnerability of the Supply Chain
The compromise of the Trivy supply chain was made possible by a prior breach of Aqua Security in late February. Despite incident response attempts, the rotation of compromised credentials was incomplete, allowing TeamPCP to regain control of the GitHub account. Aqua Security stated it is performing a more thorough cleanup of credentials. Over the weekend, the group also managed to compromise Aqua Security's Docker Hub account, publishing two malicious updates for the scanner. TeamPCP further compromised a second Aqua Security GitHub account, modifying and publishing 44 internal repositories, including source codes, Trivy forks, CI/CD pipelines, and team knowledge bases. It appears that subsequent attempts at complete credential rotation were again unsuccessful. The CanisterWorm campaign appears to be a direct extension of the initial Trivy compromise, rather than a separate operation. The worm's ability to infiltrate developer pipelines and machines represents a serious escalation of TeamPCP's campaign to steal as many credentials as possible. Development organizations should be aware they may have been affected unknowingly. Both Aikido and Socket have published indicators that organizations can use to determine if they have been targeted or compromised.
Our Publication Thinks That...
This incident highlights a concerning evolution in the tactics of malicious actors, who are increasingly exploiting the complexity and interconnectedness of modern software supply chains. TeamPCP's ability to automate large-scale attacks and integrate sophisticated control mechanisms, such as ICP canisters, demonstrates a level of competence that requires an equally advanced response from companies and security researchers. The self-propagating nature of the malware and the specific targeting of critical infrastructure like CI/CD pipelines represent an existential threat to organizations that depend on these tools. The component of the data wiper targeted at Iran adds an additional layer of complexity, suggesting possible geopolitical motivations or an attempt at misdirection. It is crucial that companies strengthen their defenses, implementing rigorous credential management practices, continuous pipeline monitoring, and thorough vetting of every software component, even the seemingly most innocuous ones. Collaboration between industry players and the rapid sharing of information on indicators of compromise are essential to counter rapidly evolving threats like this one. Cybersecurity is no longer an option but an indispensable necessity in the digital age.
Source: Original
Sponsored Protocol