In the increasingly interconnected landscape of modern technology, the convenience of remote control has established itself as a fundamental pillar for IT infrastructure management. However, this very convenience harbors a dark side, an Achilles' heel that, if exposed, can transform the most efficient operations into a cybernetic nightmare. Imagine granting almost limitless access to the pulsing heart of your systems, at the deepest level, that of the BIOS, and then exposing this privileged gateway directly to the internet. This chilling reality emerges with the recent disclosure of serious vulnerabilities affecting IP KVM devices from no less than four major global manufacturers. The question is no longer a theoretical “what could possibly go wrong?”, but a pressing and disturbing “when will it go wrong, and with what consequences?”.
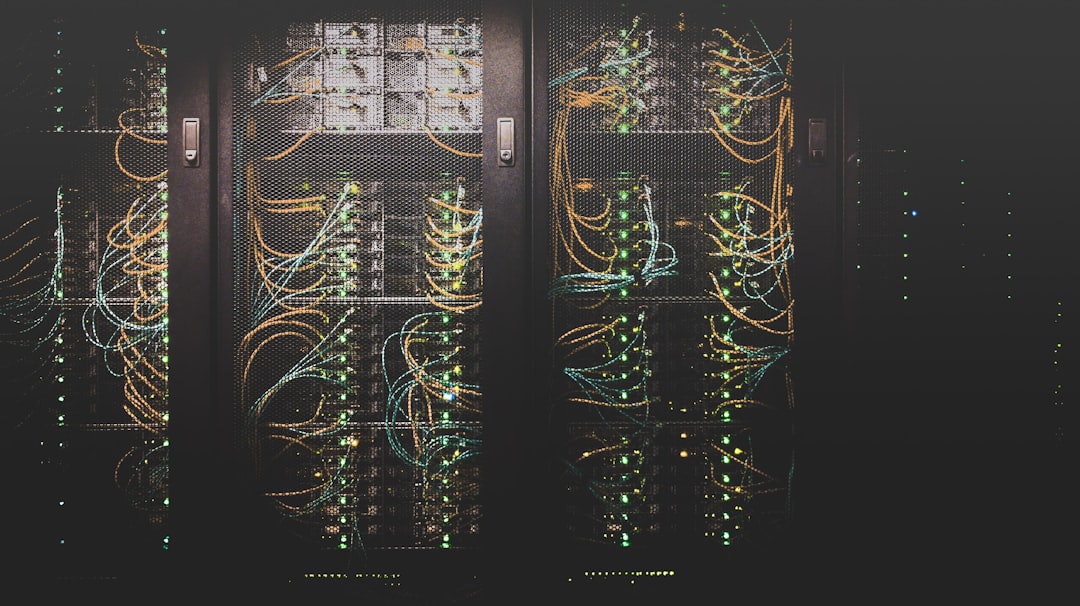
IP KVMs, an acronym for Keyboard, Video, Mouse over IP, are essential tools for remote server and data center management. They allow administrators to physically access a machine as if they were sitting in front of it, with the ability to interact with the operating system, boot from external devices, and modify BIOS settings. This incredibly powerful and necessary capability for operational continuity becomes an existential threat when the devices themselves present security flaws and are exposed without adequate protection to the vast and ruthless arena of the internet. The ease of access they offer transforms into a fast lane for sophisticated and determined attackers, ready to exploit every tiny crack in the digital armor.
In-depth research, conducted by cybersecurity experts, has revealed a series of vulnerabilities that go far beyond simple configuration errors. We are talking about critical flaws that can allow remote code execution, authentication bypass, disclosure of sensitive credentials, and unauthorized access to system data and configurations. This means that an attacker, once an internet-accessible and vulnerable IP KVM is identified, could potentially gain complete control of the connected server, regardless of the operating system or security patches applied to it. It’s a “zero-level” access, bypassing all perimeter and internal defenses, a true remote control for destruction or data theft on an industrial scale. The potential impact on businesses, governments, and critical infrastructures is, to say the least, catastrophic.
Let's consider the practical implications. For a business, a compromised IP KVM could mean a ransomware attack that entirely halts operations, the theft of priceless intellectual property, or the manipulation of industrial control systems with real physical consequences. In the context of data center management, unauthorized BIOS-level access would allow altering boot parameters, injecting persistent malware, or even completely disabling machines, causing prolonged service interruptions and astronomical financial losses. The mere convenience of not having to physically travel to a server room for low-level maintenance dramatically clashes with the risk of total compromise, a price too high to pay for superficial efficiency. The implications extend beyond a single company, touching trust in digital commerce and the stability of infrastructures that support our daily lives.
The responsibility for disclosing these vulnerabilities falls to researchers, crucial figures who work in the shadows to illuminate dangers before they are exploited on a large scale. Their meticulous work and subsequent responsible disclosure, usually in coordination with manufacturers, are fundamental steps to trigger the patching and mitigation process. However, the speed with which these patches are developed, distributed, and, most importantly, applied by end-users, is often a critical bottleneck. Many devices remain unpatched for months or even years, creating a vast attack surface that malicious actors do not hesitate to scan with automated tools and increasingly sophisticated techniques. Inertia, lack of resources, or simple unawareness of such a profound risk are among the biggest allies of cybercriminals.
So, how can we mitigate such a pervasive and potentially devastating risk? The answer lies in a multi-layered approach to security. Firstly, it is imperative that all IP KVM devices are constantly updated with the latest firmware provided by manufacturers, as soon as it becomes available. Secondly, it is absolutely crucial that these devices are never directly exposed to the internet. Remote access should be channeled exclusively through robust and securely configured VPNs (Virtual Private Networks), with mandatory multi-factor authentication (MFA). Network segmentation is another key strategy: isolating KVMs in a separate, tightly controlled network with restrictive firewall rules can drastically limit the attack surface. Regular security audits, penetration testing, and continuous IT staff training on the secure management of such devices are non-negotiable steps. Security is not a product bought once and for all, but a continuous process, a mindset that must permeate every layer of the digital infrastructure.
The lesson imparted by these discoveries about IP KVM vulnerabilities is clear and resonates as a stark warning for every organization operating in the digital age. The convenience and power of remote management tools must never, under any circumstances, compromise the fundamental principles of cybersecurity. Ignoring the inherent risks of exposing devices with BIOS-level access to the internet is like leaving the front door open to expert burglars, inviting them to take over your entire digital home. Constant vigilance, proactivity in mitigation, and an unwavering commitment to best security practices are the only defenses against a future where “what could possibly go wrong” transforms into a harsh and bitter reality. It is time to act decisively, before the shadow of vulnerabilities becomes total darkness.
Sponsored Protocol