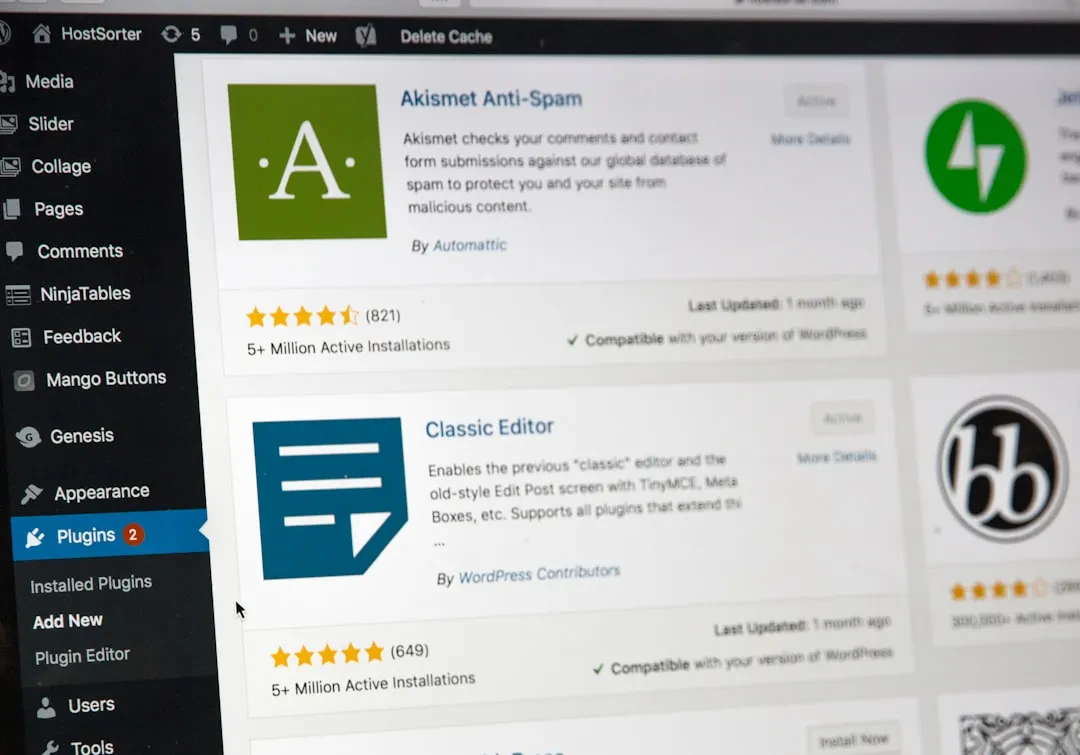
In recent months, security on WordPress has been put to the test, with many WordPress sites compromised. Some of the vulnerable plugins were among the most popular and have been targeted by cyberattacks, resulting in thousands of compromised WordPress sites. Expert hackers have exploited security flaws to gain access to sites, inject malware, and compromise data. But what does all this mean for those managing a WordPress site? And how can you defend yourself? Let's look at the situation and possible solutions together.

Compromised WordPress Sites and the Plugins Involved: What Are the Risks?
Here is a list of recently affected plugins and the vulnerabilities that made them attack targets. You might be surprised to see that even some of the most well-known plugin names were involved.
1. Jetpack
Jetpack is one of the most used plugins in the world, with millions of active installations. A recently discovered vulnerability allowed logged-in users to access data entered into forms. The team has already released a security update, so if you use Jetpack, have you already updated?
2. Frontend Registration – Contact Form 7
Contact Form 7 also took a hard hit: the vulnerability allowed some users to modify the roles assigned to other site users. Have you checked that you have installed the latest version? It's easy to forget sometimes, but updates are the first line of defense against these issues.
3. SiteTweet
Perhaps less known, SiteTweet is another vulnerable plugin, allowing hackers to insert malicious scripts. If you use this plugin, remember to update to the latest version.
4. Popup Builder
Hit by the Balada Injector malware, Popup Builder was used to infect thousands of sites. The patch is available in version 4.2.3, but have you already checked if yours is updated?
5. Happy Addons for Elementor
This plugin, loved by Elementor users, had an XSS vulnerability that allowed malicious code to be inserted with simple contributor access. Have you verified that your plugin is at version 3.10.1?
How to Protect Your WordPress Site: Are You Updated?
Security on WordPress starts first and foremost with updating plugins. We all know how easy it is to ignore the icon indicating new available updates, but it's a risky practice. Here are some practical tips to avoid nasty surprises:
• Constant Updates: Have you set your site to update plugins automatically? Many attacks target precisely outdated plugins.
• Plugin Choice: Do you use plugins you trust with a good update history? It's always better to avoid plugins that haven't received updates for too long or lack recent reviews.
• Extra Security: Are you using a comprehensive security solution? Firewalls, two-factor authentication, and activity monitoring are essential for keeping an eye on your site.
The WordPress Community: How Does It Handle These Risks?
WordPress is one of the most secure platforms precisely because of its community of developers and users. When a vulnerability is discovered, the team and plugin creators act quickly to find a solution. But we users also have an active role: applying updates and monitoring activities is essential to protect our data and that of our users.
Do you ever wonder how secure your site is? The recent wave of attacks is a reminder for all of us: security is a priority and must not be neglected.
The recent attacks on WordPress sites remind us how important it is to maintain high vigilance on security, updating regularly and choosing reliable plugins. With millions of sites relying on WordPress, each of us can do our part to keep the platform secure.
Sponsored Protocol