Cybersecurity Alarm for CopyFail
A formidable new malware, dubbed CopyFail, is emerging as the most significant threat to Linux systems in recent years. This malicious code is capable of impacting a wide range of infrastructures, from multi-tenant servers to continuous integration and continuous delivery (CI/CD) workflows, and Kubernetes containers. Its rapid spread and the potential severity of the damage have caught the global security community off guard, casting a shadow over current data protection and IT operations practices.
CopyFail's Impact on Modern Infrastructures
CopyFail's distinctiveness lies in its ability to exploit vulnerabilities often present in modern cloud and software development environments. Its architecture allows it to infiltrate Linux operating systems, a platform ubiquitous in data centers and enterprise network infrastructures. CI/CD workflows, the lifeblood of agile software development, become a particularly insidious attack vector, as the malware can compromise source code even before it is deployed. Similarly, Kubernetes containers, essential for orchestrating distributed applications, represent a critical target. Compromising these environments could lead to large-scale service disruptions, theft of sensitive data, and a compromise of the software supply chain.
The Challenge of Rapid Defense
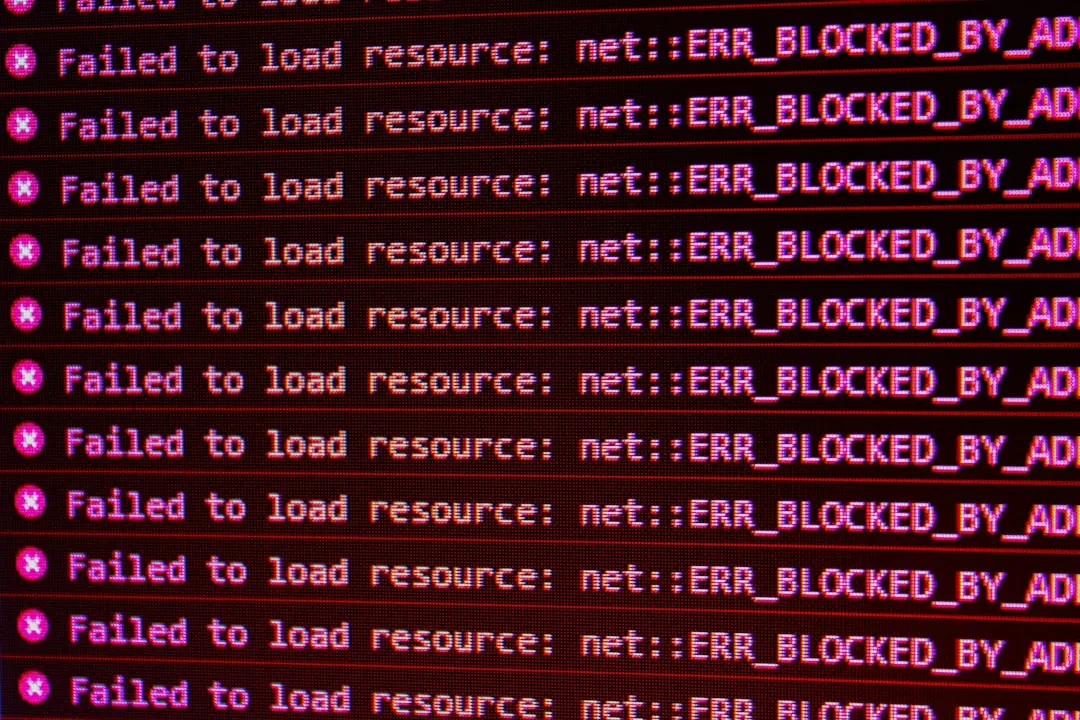
Security authorities and experts are working tirelessly to fully understand the scope of the threat and develop effective countermeasures. The nature of the malware, which appears particularly adept at evading traditional signature-based detection systems, makes defense an arduous task. It is speculated that CopyFail employs advanced obfuscation and polymorphism techniques to evade detection. This raises questions about the current preparedness of companies and the need to revise security strategies, shifting from a reactive approach to one that is proactive and based on behavioral anomaly detection. The speed with which this threat has spread, catching many by surprise, highlights the ongoing arms race in the field of cybersecurity, where defenders must constantly adapt to the evolving tactics of attackers.
Considerations for the Linux Ecosystem
The recent period has seen particular attention paid to the Linux ecosystem, not only for threats like CopyFail but also for initiatives expanding its use. An interesting example is the ability to turn the PlayStation 5 into a Linux system, demonstrating the versatility of the open-source operating system. However, this increased adoption also brings greater security responsibilities. The incidence of CopyFail underscores the critical importance of timely updates, vulnerability patching, and the implementation of robust security policies across all Linux environments, especially those handling critical workloads and sensitive data. Collaboration between security researchers, developers, and system administrators is fundamental to mitigating the risks associated with threats of this magnitude.
The Future of Cloud Security
The emergence of CopyFail is not an isolated event but part of a broader context of increasingly sophisticated cyber threats. As companies continue to migrate to the cloud and adopt container-based architectures, the security of these environments becomes paramount. Lessons learned from incidents like this will need to guide the development of new defense technologies and the adoption of more robust security practices. We are likely to see increased emphasis on security automation, artificial intelligence for threat detection, and more careful management of the software supply chain. For further insights into challenges related to security and technological evolution, one can refer to articles on legal and regulatory hurdles in technological evolution, which often parallel cybersecurity issues.
Sponsored Protocol