In the collective imagination, the
Deep Web and the
Dark Web are often a single large, dark space populated only by hackers and criminals. In reality, the two terms refer to different things, and the line between legitimate use and abuse is less cinematic and more technical than it seems. Understanding the difference and what is truly found in these layers of the web helps to reduce alarmism and focus on concrete security.
What is really meant by the Deep Web
The term
Deep Web refers to the set of online resources that are not indexed by traditional search engines. These are not necessarily illegal contents, but simply pages and services that Google, Bing, and others do not see or cannot read. The definition includes restricted areas, corporate intranets, databases accessible only via forms, and services behind authentication.
When we log into our hosting control panel, check our bank statement, or access a company SaaS dashboard, we are moving within portions of the Deep Web. These are contents invisible to crawlers but perfectly legitimate. Various informative articles, like those available on
Khan Academy or on digital culture portals, reiterate this often-ignored point in sensationalist headlines.
Why most of the web is invisible to search engines
Search engines work by following public links and analyzing pages reachable without credentials. Everything that requires authentication, a specific search in a form, or a private connection remains outside. Academic databases, legal archives, ticketing systems, and online CRMs are classic examples of Deep Web content.
From the perspective of operating systems and servers, these are often traditional web applications, protected by logins and access controls. The fact that they do not appear in Google results does not make them mysterious; they are simply not designed to be public. In many cases, the problem is actually the opposite: preventing them from accidentally ending up in search engine indexes.
What is the Dark Web and its relationship with the Deep Web
The
Dark Web is a much more specific subset of the Deep Web. It refers to services accessible only through
anonymous networks or overlay networks, like that of the
Tor project, and not via normal HTTP or HTTPS browsing. The addresses do not use classic domains but special extensions, like .onion services.
These services are not only unindexed; they are specifically designed not to be reachable from the open web. Traffic is routed through multiple nodes to make it difficult to correlate IP address, content, and location. Official documentation, such as that from the Tor Project, details the goals and limits of these networks, which were originally created also for research and privacy protection purposes.
What is really found on the Dark Web, between legal and illegal
On the
Dark Web, very different realities coexist. There are projects seeking to offer safer communication channels in authoritarian contexts, journalistic initiatives providing platforms for anonymous reporting, and mirror copies of news sites designed to bypass censorship. Organizations like
SecureDrop exemplify this use oriented towards source protection.
Alongside these positive experiences, however, exists an ecosystem of
illegal activities: black markets, money laundering services, sale of stolen data, forums dedicated to cybercrimes. Reports from entities like
Europol or national security agencies have been analyzing these dynamics for years without indulging in the simplifications that often emerge in popular narratives. The Dark Web is not only about crime, but it is certainly one of the spaces where some forms of digital crime operate with more freedom.
Real risks: malware, scams, and monitoring
Beyond the legal dimension, there is a more immediate level for cybersecurity. Browsing in poorly controlled environments exposes users to
malware, advanced phishing, and well-crafted scams. Seemingly harmless files can hide malicious code, professional-looking services can be traps built to steal credentials, cryptocurrencies, or sensitive data.
Law enforcement agencies and national CERTs themselves remind us that no network guarantees absolute anonymity. Configuration errors, imprudent behavior, and cross-referencing of different data can reconstruct identities and activity trails. Investigations into illegal marketplaces shut down in recent years show how often it was precisely small technical details that allowed for identifications and arrests.
Why confusing the Deep Web and Dark Web is a problem
Putting everything in the same pot does double damage. On one hand, it fuels the perception that every unindexed portion of the web is suspicious, including legitimate services handling sensitive data. On the other hand, it risks trivializing the real problems of
cybercrime, confusing morbid fascination with the exotic and awareness of concrete threats.
For those involved in
operating systems and security, distinguishing between these levels is fundamental. Protecting applications on the Deep Web involves access controls, server hardening, log management, and proper encryption in transit and at rest. Understanding the Dark Web, however, helps monitor the circulation of stolen data, the evolution of attacker tools, and the presence of hostile infrastructure.
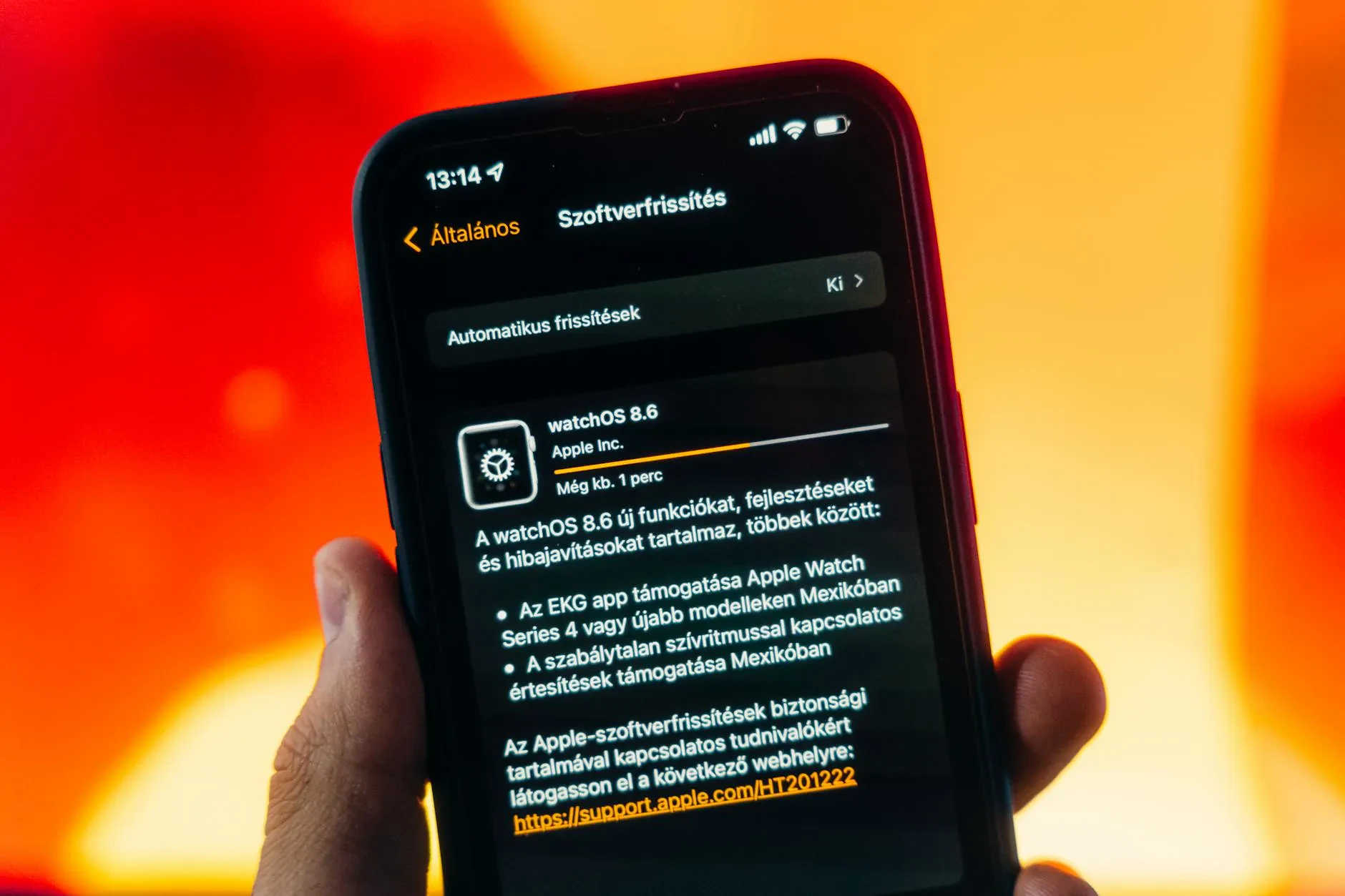
Operating systems, browsers, and layers of defense
Modern operating systems and browsers already integrate various layers of defense designed to reduce risks even when browsing in potentially dangerous contexts. Sandboxing, frequent updates, blocking of obsolete components, warnings about suspicious certificates, and lists of known malicious sites are examples of basic barriers.
These protections, however, do not replace users' conscious choices. Unupdated software, randomly installed extensions, and inattention to downloads and attachments open gaps that no operating system can close alone. From an enterprise security perspective, monitoring the use of unauthorized tools and training people to recognize risk signals remains as essential as correctly configuring firewalls and proxies.
Digital awareness beyond the myth of the dark internet
The fascination with the dark side of the web is understandable, but it often hides a more concrete problem: the lack of basic digital literacy. Understanding what we call the
Deep Web and what instead belongs to the
Dark Web helps to downsize myths and fears and focus on realistic security practices: backups, updates, credential management, careful use of online services.
The web is not a homogeneous and neutral place, but a set of layers, protocols, communities, and regulations. Knowing where the indexed web ends and where the spaces more difficult to control begin means having a more precise map of the territory we navigate every day, with the browser open on the desk or the smartphone in hand.